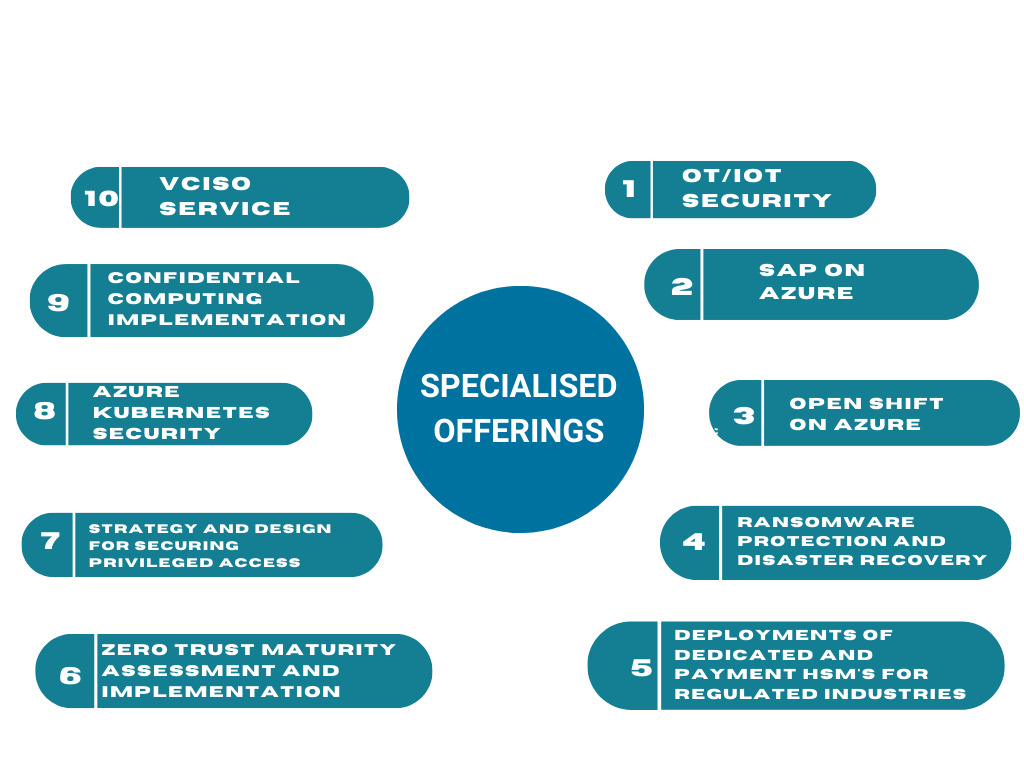
Specialised Offerings
Techsolve Consulting provides a diverse array of specialized services to tackle contemporary technological challenges.
OUR SERVICES
Helping Organizations Protect Their Data and Systems
VCISO – Virtual Chief Information Security Officer as a Service
Vciso - Your CISO's time-saving ally! Eliminate manual tracking and allocation tasks with our advanced tool. Scan vulnerabilities, track audits, and classify risks based on severity effortlessly. Stay within a single platform, avoiding unnecessary tool switching. Empower your cybersecurity team, make informed decisions, and enhance your organization's security posture. Embrace automation and save time with Vciso - the ultimate solution for efficient vulnerability management. Stay protected, stay productive!
Zero Trust Maturity Assessment and Implementation
Zero-Trust has become the DeFacto target state Security Architecture of Enterprises, small, medium and large, their Enterprise security practices driven by NIST or otherwise. We help the organizations understand their current Zero Trust maturity state using our Zero Trust Maturity assessment practices that would help them understand the areas of critical issues and decide their next steps as far as corrective actions are concerned. We would also partner with the customer teams and implement Zero Trust either using RAMP (Rapid Modernization Plan) or the detailed Deployment processes.
Strategy and Design for Securing Privileged Access
Majority of the cyber-attacks have “Privilege escalation” as a common step in the attack path, targeting high-privilege accounts. We have carefully crafted a security architecture for Securing Privileged access using the design principles of Privileged Access management (PAM) and Privileged Identity Management and combining those with the security policies for endpoints, intermediaries, interfaces and the highly secured target networks and data. We also go a step further in implementing simulated attacks to test the effectiveness of the Privileged Access Strategy, using MITRE TTPs.

Ransomware Protection and Disaster Recovery
Our holistic security Strategy includes a separate section for Business Security Resilience. We design the security policies and controls to avoid falling prey to ransomware attacks. In the event of a successful attack, we work with the business teams and Microsoft’s DART to make sure that the impact of the attack is minimal, there is no lateral movement and there is less to no impact to the business operations. We have carefully crafted a security architecture that would help you build your Backup and Recovery mechanisms for DR during ransomware attacks. We also work with the business teams to complete the feed-back loops in updating the playbooks, DR drills, MITRE attacks simulations and ransomware education.
Deployments of Dedicated and Payment HSMs for regulated industries
Customers in the regulated sectors that have migrated their secure workloads to the cloud now would have a need to migrate their HSM solution to Azure or implement a Dedicated FIPS 140-2 Level 3 HSM or FIPS 140-2 Level 3, PCI HSM v3 Payment HSMs. We help in completing this leg of customer’s “Secure Cloud Transformation” by migrating or deploying green field Dedicated or Payment HSMs on Azure and integrating the same with the consuming workloads that involves complex processes.
Securing Kubernetes Workloads
Implementing production grade workloads on Kubernetes has always been nothing short of complicated. Majority of the product organizations and the likes of them face a great deal of difficulty in setting up the Kubernetes workloads that are spread across hybrid environments and host multi-tenant applications. We help customers design their K8s workloads in the most secure way based on our 360-degree Cybersecurity Strategy, where in the security is designed across multiple layers of defense using Azure services and policies targeting the container workloads. We provide a matrix of the security controls mapped to varied phases and required frameworks so as to empower you to maintain the workloads with less efforts.
Implementation of SAP On Azure
Migration of the business-critical workloads such as SAP has to be done with a great deal of precision and a careful evaluation of the ROI on migrating to the cloud. We help our enterprise customers who need to either migrate their SAP systems from on-premises or from other clouds or implement SAP afresh on Azure. We along with Enpersol, our co-implementation partner, can help you complete the implementation of your SAP systems on Azure using industry proven and the best architectural practices.

Implementation of Confidential Computing
We work with customers who want to use Confidential computing either using Secure Enclaves or Confidential VMs and implement the feature for their workloads that run need to run on VMs or Kubernetes i.e., AKS. We also help customers implement “Clean room” scenarios from the scratch or implement any of the vendor solutions from the marketplace. These include Beekeeper AI, Decentriq etc.

OpenShift on Azure
Mature organizations such as Airbnb and Netflix that have been using the container technologies for a while have developed platform engineering as a culture to ease the work of the developers and the infrastructure or DevOps teams. If you are one such organization with different teams owning and managing different pieces of your Kubernetes environments, then we can help you implement Azure Redhat Openshift (ARO), a Kubernetes platform on Azure. Rest assured that the transition from your Kubernetes experiments in the sandbox environments to implementing ARO in Dev and Prod environments would be made easy with our validated processes.

OT /IOT Security
Securing OT systems have not been as easy as securing IT. The significant issues include Legacy Systems with outdated technologies, Air-gapped environments, lack or absence of patching and emphasis on Safety more than anything else. Our solution is based on Microsoft Defender for IOT that helps customers monitor their OT network traffic and apply the latest OT threat intelligence to avoid attacks. We also make the security holistic by implementing a) Securing Privileged access b) Defender for Endpoint solution c) Backup of the OT client systems and d) Implementation of Micro-segmentation for controlled network access. We have our co-implementation Partner “Beacon Security Systems” working with us to implement solution and educate the customers of the latest threats and ways to handle them.